How to Build Role-Based Access Control in SaaS Products
A founder-focused guide to building RBAC in SaaS: when to add it, how to scope it, and how to avoid over-building permissions early.
Key Takeaways
- 01
RBAC works best when you start with 2-4 roles that match real user types. Avoid over-building early.
- 02
Short answer: Start with admin, user, viewer. Defer granular permissions. Add when usage proves the need.
- 03
Strong RBAC scope comes from matching roles to user types. Do not build for hypothetical enterprise needs in MVP.
- 04
Shorter, clearer sections make the article easier to scan and easier for buyers to act on.
- 05
Common founder mistake: Over-building RBAC for hypothetical enterprise needs. Start with 2-4 roles.
- 06
The best next step is usually to list user types and map to 2-4 roles.
How to Build Role-Based Access Control in SaaS Products matters because buyers do not reward software that is only technically correct. They reward software that solves a real workflow, looks credible, and is easy to evaluate. A founder-focused guide to RBAC in SaaS.
If you are researching RBAC, the useful questions are practical ones: what should be built first, what should be delayed, where does the budget really move, and which tradeoffs are worth making now. That is the frame this guide uses.
Quick answer
RBAC works best when you start with 2-4 roles that match real user types. Avoid over-building permissions early. Add granular roles when usage proves the need.
- Start: 2-4 roles (admin, user, viewer).
- Defer: granular permissions, custom roles per user.
- Scope: what does each role need to see and do?
Who this guide is for
This article is for founders and buyers building RBAC in SaaS products.
It is written to help teams scope RBAC without over-building.
- Useful when the backlog is larger than the budget.
- Useful when the founder needs to cut scope without losing the product thesis.
- Useful when the first release must support customer conversations, pilots, or revenue.
RBAC scope by stage
The goal is not to create more theory. The goal is to show the right scope for each stage.
| Stage | Roles | What to include | What to defer |
|---|---|---|---|
| MVP | 2-4 roles | Admin, user, maybe viewer | Granular permissions, custom roles |
| Growth | 4-6 roles | Role-based views, actions | Per-user overrides |
| Enterprise | Custom | Granular, custom roles | — |
How to scope RBAC
The first release should prove something concrete: that a buyer will care, that a user will adopt the workflow, or that the product can replace a painful manual process. Without that frame, the build drifts into generic software effort.
Define roles from user types
Who are the users? Admin, user, viewer. Map each to what they need to see and do.
Start with coarse-grained
Role-based access (admin sees everything, user sees their stuff). Defer permission-level granularity.
Add granular when needed
When usage proves the need for granular permissions, add them. Do not build for hypothetical enterprise needs in MVP.
Common founder mistake
The common mistake is over-building RBAC for hypothetical enterprise needs. Start with 2-4 roles. Add granular when usage proves the need.
Founder note
When RBAC is genuinely complex (multi-tenant, many roles), early software consulting input can help scope. But for most MVPs, 2-4 roles suffice.
RBAC checklist
- List user types. Map to roles (admin, user, viewer).
- Define what each role can see and do.
- Start with 2-4 roles. Coarse-grained.
- Defer granular permissions, custom roles per user.
- Add granular when usage proves the need.
What to do next
If you are importing these JSON files into MongoDB, this is the content shape you want: clean headings, clear box sections, visible lists, and one practical table.
Apply this in a real project
If you’re planning to build or improve software based on these ideas, our custom software development services can help you define scope, reduce delivery risk, and ship maintainable systems.
For founder-led execution, explore our product development services and web development services to turn requirements into a working release with clear ownership.
Expert Insights
Start with 2-4 roles
Admin, user, viewer. Map to real user types. Coarse-grained. Defer granular permissions until usage proves the need.
Do not build for hypothetical enterprise
Enterprise RBAC (granular permissions, custom roles) can wait. Add when you have enterprise customers and evidence of need.
Role-based views, not just actions
RBAC is not just about actions. What can each role see? Role-based views and data filtering matter as much as actions.
Reader Rating
Based on 1 reviews
Frequently Asked Questions
How many roles should I start with for RBAC?+
What should I include in MVP RBAC?+
When should I add granular permissions?+
What is the biggest RBAC mistake?+
How much does RBAC add to development cost?+
Reader Questions
How do I know what roles I need?
List user types. Who are they? Admin, user, viewer. Map each to what they need to see and do. Start with 2-4.
What part of RBAC should I focus on as a founder?
Focus on role definition and what each role can see. Defer granular permissions. Add when usage proves the need.
Can I add RBAC later?
Yes, but it is easier to design for it early. Add roles and checks from the start. Keep it simple. Add granular later.
Related Articles
Technology • 3 min
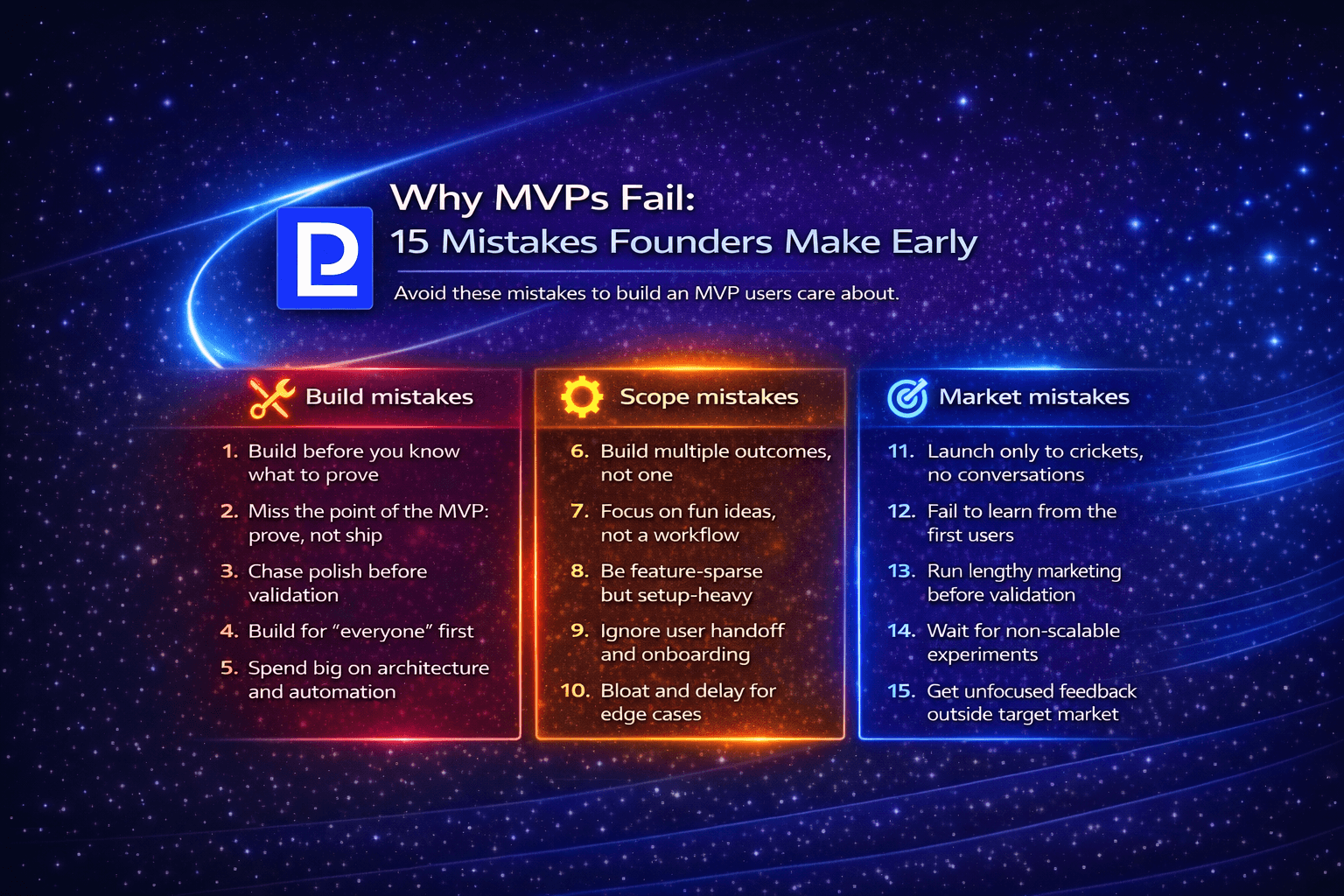
Why MVPs Fail: 15 Mistakes Founders Make Early
A founder-focused guide to the 15 most common MVP mistakes: what causes failure, how to avoid them, and how to build MVPs that actually validate.
Technology • 3 min
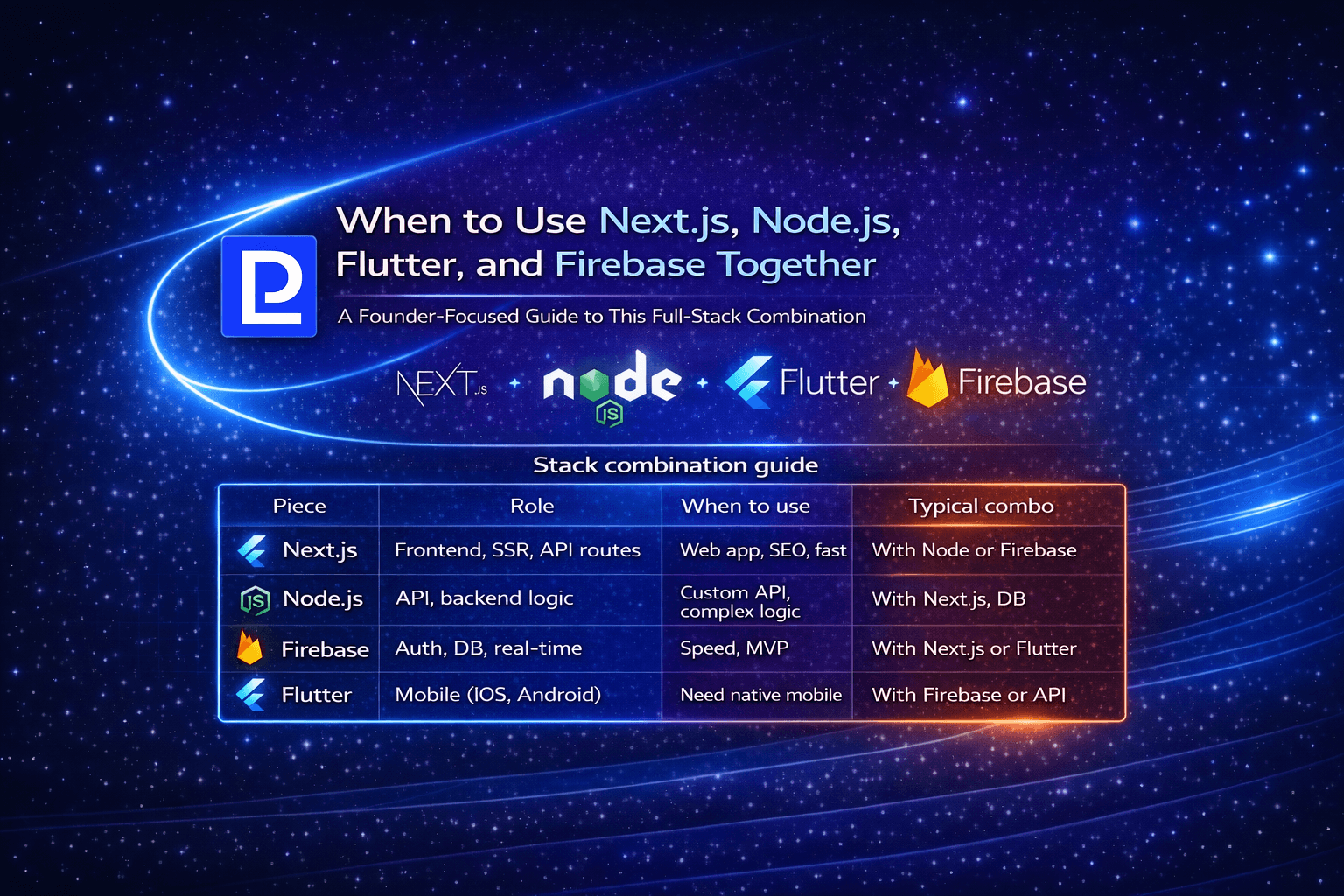
When to Use Next.js, Node.js, Flutter, and Firebase Together
A founder-focused guide to combining Next.js, Node.js, Flutter, and Firebase: when the stack makes sense and how to use them together.
Technology • 3 min
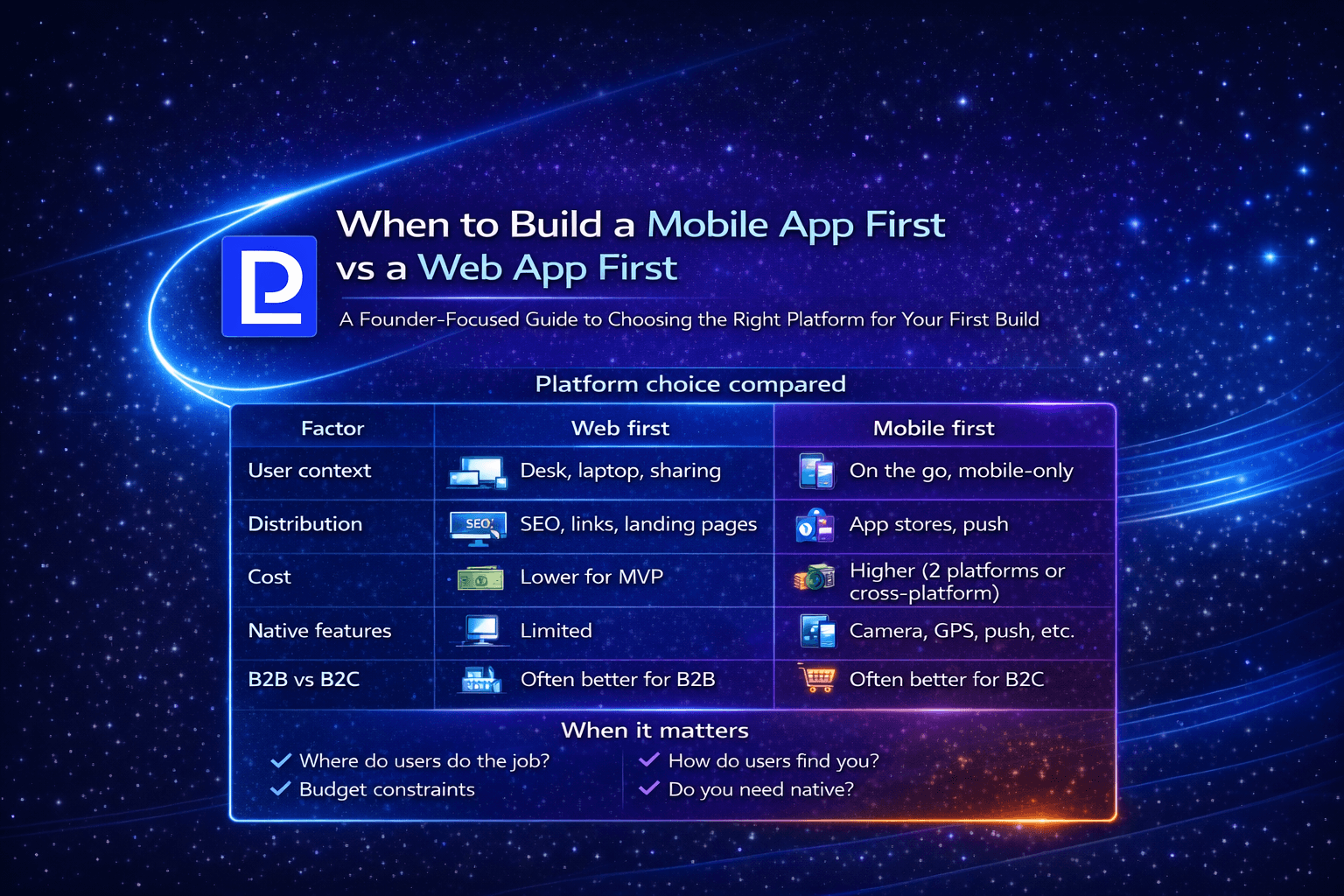
When to Build a Mobile App First vs a Web App First
A founder-focused guide to choosing mobile-first vs web-first: when each makes sense, tradeoffs, and how to decide for your product.